THE PROMPT for Microsoft Security - Issue #63
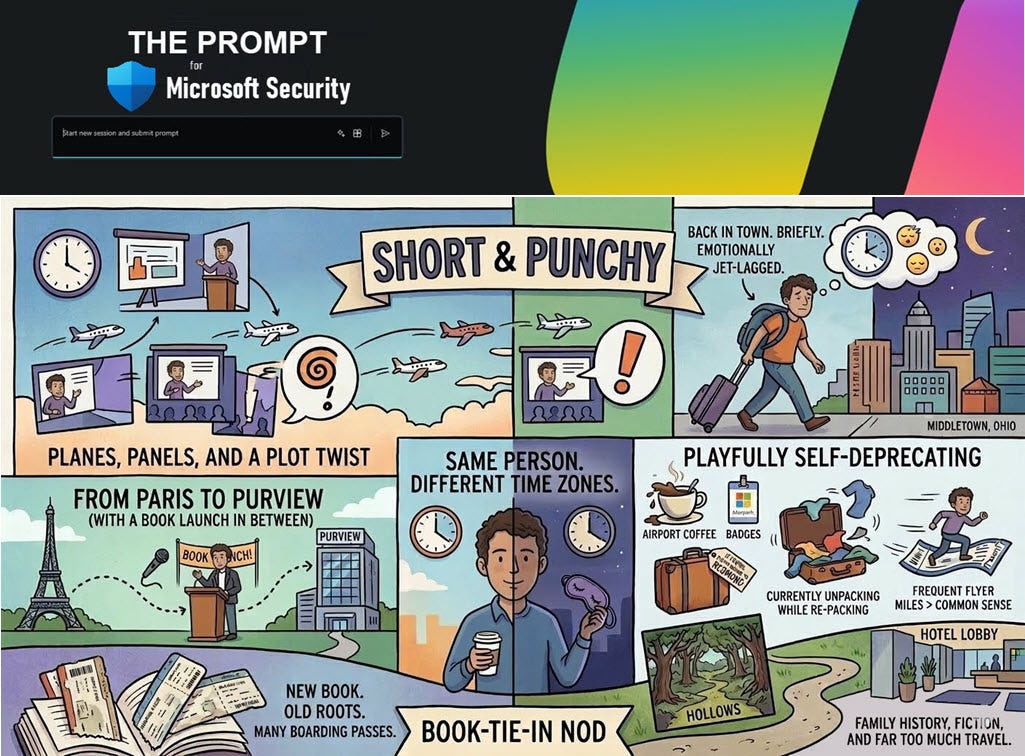
Planes, Panels, and a Plot Twist
Things from Me
Happy Friday everyone!
We’re back! Did you miss me?
After nearly a month of planes, trains, and very questionable airport coffee, I’m finally back in the office for a couple of weeks. It’s been a whirlwind tour—Paris, Denmark for Experts Live, Redmond, and now (briefly) home—before I pack up again and head back to Redmond for the MVP Summit in just a couple of weeks. Apparently, I really like frequent‑flyer miles.
Between the travel and events, one other milestone worth sharing: I’ve released a new book. Shadows in the Hollows is a work of fiction, but it’s deeply rooted in my family’s culture and history and explores the often‑overlooked story of the Melungeon people. If you’re curious, you can find it here: https://amzn.to/4sAYwNf
Additionally, I had some downtime once I returned to catch a breath, but also release version 4.0.4 of the Garmin Chat Desktop app. Details HERE. This version adds support for Ollama, the latest Claude models, and more activities (from 10 to 50).
More to come—after I unpack. Again.
Talk soon.
-Rod
Things that are Related
Secure agentic AI for your Frontier Transformation - Today we shared the next step to make Frontier Transformation real for customers across every industry with Wave 3 of Microsoft 365 Copilot, Microsoft Agent 365, and Microsoft 365 E7: The Frontier Suite.
Comprehensive Security in the Era of AI: What Nonprofits Need to Know Now - Microsoft’s guide, Comprehensive Security in the Era of AI, offers nonprofits a clear, compassionate roadmap for navigating this moment of change. Below is a mission‑focused summary of the guide’s key insights and how they apply directly to the nonprofit sector.
Things to Watch/Listen To
The Purview Practitioner (podcast) - Everyone’s racing to get AI deployed - Copilot, agents, all of it. But the moment you switch this stuff on, it finds everything. Every bit of permission drift, every folder somebody shared five years ago, every sensitive document sitting somewhere it shouldn’t be. This podcast takes you through a real data security journey - from visibility and classification through to DLP, governance, and enabling AI without it all falling apart. Short episodes, practical advice, no jargon.
Security Copilot Things
Introducing Agentic Secret Finder: Finding Real Credentials Where Traditional Tools Fail - Agentic Secret Finder (ASF) is an AI-powered capability in Microsoft Security Copilot that detects leaked credentials in unstructured content, such as emails, chat logs, documents, and screenshots, where traditional pattern-matching tools struggle. Agentic Secret Finder (ASF) is “agentic” because it relies on a multi‑step, multi‑agent reasoning workflow rather than a single pass detector. Detection, verification, and contextual analysis are handled by distinct reasoning stages, allowing ASF to find real credentials without flooding users with false positives. Unlike regex-based scanners, ASF uses reasoning to identify not just credentials, but the systems they unlock, helping security teams understand exposure and respond faster. In benchmark testing on synthetic datasets, ASF achieved 98.33% true credential detection with zero false alarms on realistic emails, chats, notes, and documents—while traditional regex scanners detected only about 40% of the same credentials. ASF is now generally available in Security Copilot, supporting 20+ credential types with high precision and actionable context.
Microsoft Sentinel Things
Microsoft Sentinel Cost Estimation And Optimization — The Definitive Guide! - By the end of this comprehensive guide, you’ll learn proven techniques from working with a large number of customers after putting so many hours into this to accurately forecast costs, implement data filtering, and leverage automation to reduce overhead while maintaining full security visibility and compliance. This guide is ideal for security architects and financial decision-makers (CFOs) seeking to achieve predictable security budgets using Microsoft Sentinel as the platform, enabling deeper planning.
Sentinel MITRE ATT&CK Coverage Analyzer - Analyze your Microsoft Sentinel analytical rules and Defender custom detection rules to generate comprehensive MITRE ATT&CK coverage reports with beautiful visualizations, including interactive radar charts, MITRE Navigator heatmaps, table optimization insights, and executive summaries.
Defender for Cloud Things
Modern Database Protection: From Visibility to Threat Detection with Microsoft Defender for Cloud - Databases sit at the heart of modern businesses. They support everyday apps, reports and AI tools. For example, any time you engage a site that requires a username and password, there is a database at the back end that stores your login information. As organizations adopt multi-cloud and hybrid architectures, databases are generated all the time, creating database sprawl. As a result, tracking and managing every database, catching misconfigurations and vulnerabilities, knowing where sensitive information lives, all becomes increasingly difficult leaving a huge security gap. And because companies store their most valuable data, like your login information, credit card and social security numbers, in databases, databases are the main target for threat actors.
Defender for Office Things
From transparency to action: What the latest Microsoft email security benchmark reveals - Today, we’re continuing that conversation. With the latest Microsoft benchmarking data, we’re sharing what real-world telemetry reveals about how effectively modern email threats are detected, mitigated, and stopped by Microsoft Defender, secure email gateway (SEG) providers, and integrated cloud email security (ICES) solutions.
Defender for Endpoint Things
Introducing effective settings: See security configurations enforced on your device - Security teams spend significant time defining policies for Microsoft Defender security settings. But when it comes to investigations or troubleshooting, the real question is often simple: what is currently being enforced on this device? Today, we’re excited to share that the settings experience is now generally available in Defender to provide this critical visibility.
Defender XDR Things
Introducing MS Defender Scout - Today, I’m excited to announce MS Defender Scout - an open-source PowerShell tool that brings AI-assisted Advanced Hunting to your security operations.
When Trust Becomes the Attack Vector: Analysis of the EmEditor Supply-Chain Compromise - There are countless security vulnerabilities and trust in software distribution is one of them. Users install applications from official vendor websites, enterprise controls allowlist signed software, and automated update mechanisms routinely pull code from trusted infrastructure. This post takes you through a supply-chain compromise targeting the EmEditor software distribution channel, where attackers weaponized a trusted WordPress-based download infrastructure to selectively deliver a trojanized MSI installer. It demonstrates how conditional server-side logic, installer abuse, and living-off-the-land techniques can bypass traditional defenses and enable credential theft at scale. It includes how the malicious installer behaved, and how defenders can detect and mitigate similar threats.
Storm-2561 uses SEO poisoning to distribute fake VPN clients for credential theft - In mid-January 2026, Microsoft Defender Experts identified a credential theft campaign that uses fake virtual private network (VPN) clients distributed through search engine optimization (SEO) poisoning. The campaign redirects users searching for legitimate enterprise software to malicious ZIP files on attacker-controlled websites to deploy digitally signed trojans that masquerade as trusted VPN clients while harvesting VPN credentials. Microsoft Threat Intelligence attributes this activity to the cybercriminal threat actor Storm-2561.
Defender Experts Things
Contagious Interview: Malware delivered through fake developer job interviews - Microsoft Defender Experts has observed the Contagious Interview campaign, a sophisticated social engineering operation active since at least December 2022. Microsoft continues to detect activity associated with this campaign in recent customer environments, targeting software developers at enterprise solution providers and media and communications firms by abusing the trust inherent in modern recruitment workflows.
Microsoft Purview Things
Purview Community: Call for Sessions! - Microsoft Purview Community Lighting Talks is a virtual event series featuring real-world demos, tips, and solutions directly from you, the Purview Community! The goal of these short, fluff-free lighting sessions is to foster authentic knowledge sharing, community connection, and highlight real experiences to empower others who use Microsoft Purview. The virtual events will be held in a simu-live format across multiple time zones and will include subject-matter experts and the speakers in a live-chat Q&A for community participation.
Microsoft Purview MVP Map - Find your favorite (or all) Purview MVPs using this MVP-developed, interactive map.
Detecting and analyzing prompt abuse in AI tools - Prompt abuse has emerged as a critical security concern, with prompt injection recognized as one of the most significant vulnerabilities in the 2025 OWASP guidance for Large Language Model (LLM) Applications. Prompt abuse occurs when someone intentionally crafts inputs to make an AI system perform actions it was not designed to do, such as attempting to access sensitive information or overriding built-in safety instructions. Detecting abuse is challenging because it exploits natural language, like subtle differences in phrasing, which can manipulate AI behavior while leaving no obvious trace. Without proper logging and telemetry, attempts to access or summarize sensitive information can go unnoticed.