Things from Me
Happy Friday everyone!
As you’re reading this, I’m probably on my morning run near Sugarcreek, Ohio which is deep in Ohio Amish country. I regularly visit here to see my best friend who is a chiropractor to the Amish. We’ve been best friends since 6th grade (1979), which, according to my calculations is around 44 years. My friend likes to tease my wife that he’s known me longer than she has. He’s the kind of friend that when together we always immediately slip back to our 12-year-old selves like no time has passed. I laugh till my cheeks and stomach hurt. It’s more family than friendship.
I do love taking vacations to the beach, but for my money a visit to Amish country sets things right better than anything and gets me energized for what’s to come. With some busy work coming helping plan for Microsoft Ignite in November, this trip hits the spot.
DON’T MISS THIS: Due to my time off, this newsletter will not next week. So, there will be no newsletter delivery on Friday, September 1st. The newsletter will pick back up delivery on Friday, September 8th.
…
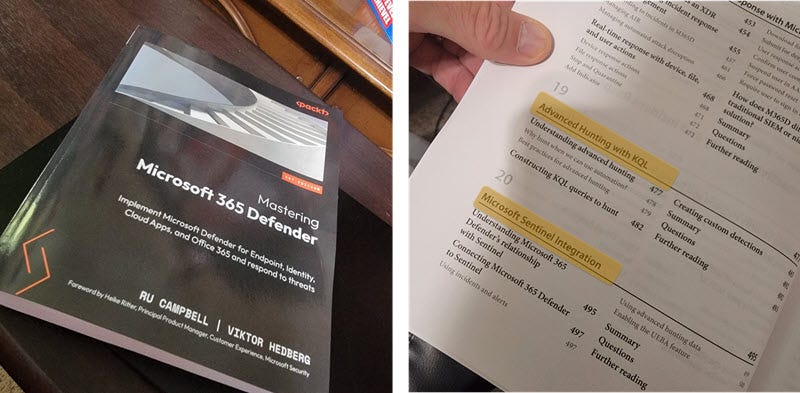
I'm an eBook kinda person, so I had read this electronically already. However, a physical copy showed up recently (thanks, Packt!) and reminded me how valuable this book is - particularly for anyone who has to work with ALL the Microsoft Defender-ized products.
Generally, you have to acquire a single book for each product. This book lumps them all together, but in a way that you don't feel you're missing out. Whether you like an electronic or physical copy, this is a worthy library addition.
P.S. I'm working to figure out how to give this physical copy away.
…
There’s a certification announcement this week I thought worth mentioning. During my Denver trip a few weeks ago, someone told me this was coming, and I just kept waiting and waiting for the official announcement before saying anything about it. In fact, I waited for this feature to materialize before taking AI-102.
The news? There’s now a button in the exams software that gives you access to Microsoft Learn during Microsoft Certification exams! Not exactly like an open-book test, but it’s a great way to research those questions you save to review later. I believe this will help drive a lot more people taking exams that were reluctant before.
Read about the details: Introducing a new resource for all role-based Microsoft Certification exams
P.S. I passed AI-102 on Tuesday. And even though I purposely waited for the Microsoft Learn feature, I didn’t need it. I passed it with an 803 score, which is the best score of any exam I’ve ever taken. Go me.
…
That’s it for me for this week.
Talk in a couple weeks.
-Rod
Things that are Related
Strengthening Your Defenses: Simulation Testing for Azure DDoS Protection - In the battle against Distributed Denial of Service (DDoS) attacks, it is crucial to have robust protection mechanisms in place. Azure DDoS Protection provides a powerful shield for your infrastructure, but how can you ensure it can handle real-world scenarios? This blog post walks you through DDoS simulation testing and its role in evaluating and enhancing Azure DDoS Protection. Discover how simulation testing can fortify your defenses and enable you to confidently withstand DDoS attacks.
Security 101 - Deepen your security knowledge and gain a fundamental understanding of a variety of cybersecurity, identity, and compliance topics and best practices.
Things to Watch/Listen To
Things to Attend
What's new in the Defender for Endpoint configuration management space? - Mon, Sep 11, 2023, 12:00 PM - 12:30 PM (your local time)
Defender for Endpoint configuration management deep dive - Wed, Sep 13, 2023, 12:00 PM - 12:30 PM (your local time)
Things in Techcommunity
Security alerts in Microsoft defender for Cloud - We have received below security alert in Microsoft defender for cloud for our App service.
NMap scanning detected (for this we got the carrier and organization as Microsoft)
Vulnerability scanner detected
Suspicious User Agent detected
AddOrRemoveTagForMultipleMachines api limitation when machine id doesn't exist - I have noticed when using the Defender for endpoint api for AddOrRemoveTagForMultipleMachines that the whole task fails to add/remove tag if one of the device IDs array is inactive or not found anymore.
Things from Partners
Generative AI Takes Center Stage at Black Hat - Generative Artificial Intelligence (AI) was the dominant theme at Black Hat 2023 in Las Vegas. Attendees could tell what they were in for, given that about 30 presentations mentioned AI or Large Language Models (LLM) in the title or description.
Defender for Cloud Things
Extended properties in Defender for Cloud security alerts are masked from activity logs - We recently changed the way security alerts and activity logs are integrated. To better protect sensitive customer information, we no longer include this information in activity logs. Instead, we mask it with asterisks. However, this information is still available through the alerts API, continuous export, and the Defender for Cloud portal.
Defender for APIs Better Together with Azure Web Application Firewall and Azure API Management - Under the Microsoft Defender for Cloud umbrella, Microsoft Defender for APIs, offers protection for APIs at every stage of their lifecycle. This service enhances the protections from Web Application Firewalls and API Gateways, resulting in a comprehensive security framework for API endpoints. In this article, we'll dive deeper into how Defender for APIs augments the security offered by Azure Web Application Firewall (Azure WAF) and Azure API Management (APIM).
Preview release of GCP support in Defender CSPM - We're announcing the preview release of the Defender CSPM contextual cloud security graph and attack path analysis with support for GCP resources. You can leverage the power of Defender CSPM for comprehensive visibility and intelligent cloud security across GCP resources.
Key features of our GCP support include:
Attack path analysis - Understand the potential routes attackers might take.
Cloud security explorer - Proactively identify security risks by running graph-based queries on the security graph.
Agentless scanning - Scan servers and identify secrets and vulnerabilities without installing an agent.
Data-aware security posture - Discover and remediate risks to sensitive data in Google Cloud Storage buckets.
Learn more about Defender CSPM plan options.
Defender for Endpoint Things
How to troubleshoot Live Response in Defender for Endpoint - Live Response is a powerful feature as part of the Microsoft 365 Defender portal. With the use of Live Response Security Operations Teams can establish a remote session to collect more files/ or forensic evidence/ run scripts remotely.
365 Defender Things
Configure Just-in-Time Access to M365 Defender - Microsoft 365 Defender RBAC offers centralized permissions management for the following services:
Defender for Endpoint
Defender for Identity
Defender for Cloud Apps
Defender for Office 365
Microsoft Defender Vulnerability Management
Secure score
#MicrosoftDefender #Security #MicrosoftSecurity #Cybersecurity #M365D
Defender for Identity Things
Managing Microsoft Defender for Identity - Comprehensive Guide - In the rapidly evolving landscape of cybersecurity, safeguarding sensitive information and digital assets is paramount. One of the powerful tools in this endeavor is Microsoft Defender for Identity.
Defender for Office Things
Send "How-to guides" to your organization from Attack Simulation training - We are thrilled to announce that Attack Simulation Training now includes an exciting new feature: "How-to Guides" that can be sent to users to provide instructions to recipient on how to complete important security tasks.
Microsoft Entra Things
Microsoft Entra Private Access — secure any app with Conditional Access - This short post will explain the new capabilities of Microsoft Entra Private Access to:
Enable access to internal apps and protocols when connected with the Global Secure Access client
Secure access with Conditional Access
Microsoft Entra Workload ID - Lifecycle Management and Operational Monitoring - Workload identities should be covered by lifecycle management and processes to avoid identity risks such as over-privileged permissions but also inactive (stale) accounts. Regular review of the provisioned non-human identities and permissions should be part of identity operations. In this article, we will go through the different lifecycle phases and other aspects to workload identities in your Microsoft Entra environment.
Introducing a New Flexible Way of Bringing Identities from Any Source into Microsoft Entra ID - I'm thrilled to announce that Microsoft Entra API-driven provisioning is now in public preview!
With today’s announcement, we’re expanding our support for HR-driven provisioning to address the most common customer asks, including:
Automatically provisioning cloud-only users and hybrid users (users that require an on-premises Active Directory account) from any trusted source
Importing data from sources like CSV files and SQL staging tables using the automation tool of your choice
Simplifying the integration by using standard SCIM schema attributes to abstract schema differences across systems and provide a consistent mapping experience
Leveraging Lifecycle Workflows to automate joiner-mover-leaver workflows for users sourced from any system of record
Fun Thing This Week
Generate music with AI - Songburst is an AI song maker built for everyone. Make music for your online content like videos and podcasts, generate samples to use in your own mixes, or export your songs to Spotify and Apple Music.